Certificate User Domains
You can use certificates as the authentication method for a new Domain.
Prerequisite
Before you can assign a specific certificate to a new Certificate User as a Client Certificate Chain, you must upload it in the Client Auth Certificates section to make the certificate available for assignment. This step can be performed by a Signum Administrator.
Configure Certificate Users Domain
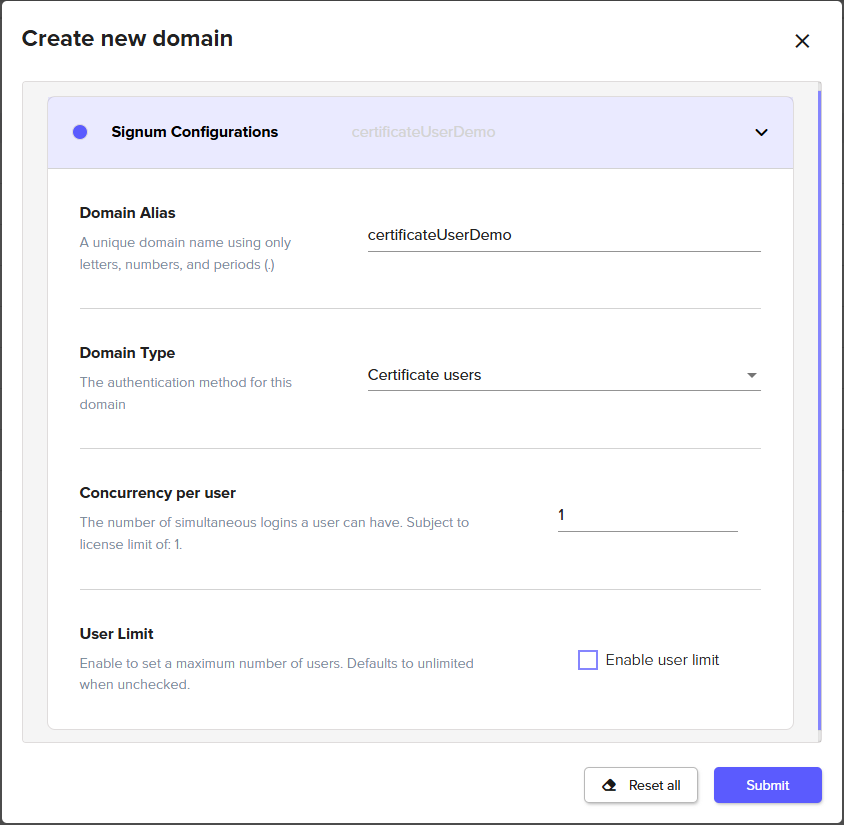
Create a new Domain in the Access tab, and select Certificate users as the Domain Type.
Configure a Certificate Users domain by selecting your desired settings and clicking Submit:
The new domain appears in the list on the Domains tab, where you can create and manage its users.
Creating a Certificate User
Select the new Certificate Users domain from the list of available domains in the Domains tab.
In the popup window for editing the domain, navigate to the Users tab.
Click New to begin creating a new user.
Set the user configuration options in Signum.
You can also set:
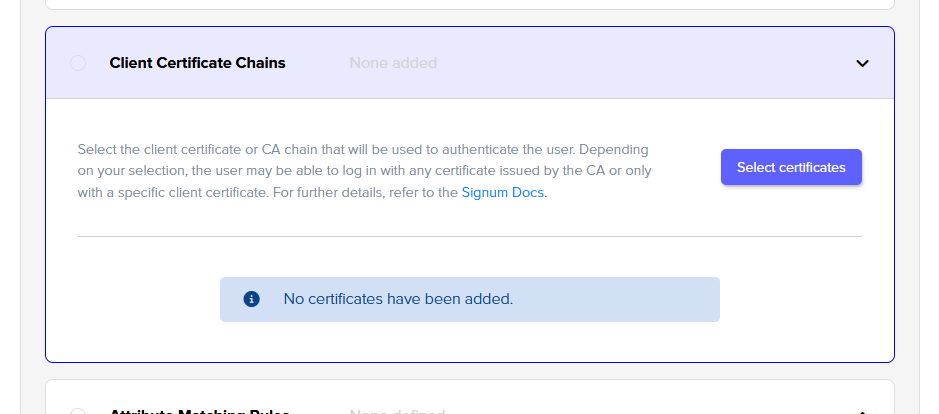
Add one or more Client Certificate Chains.
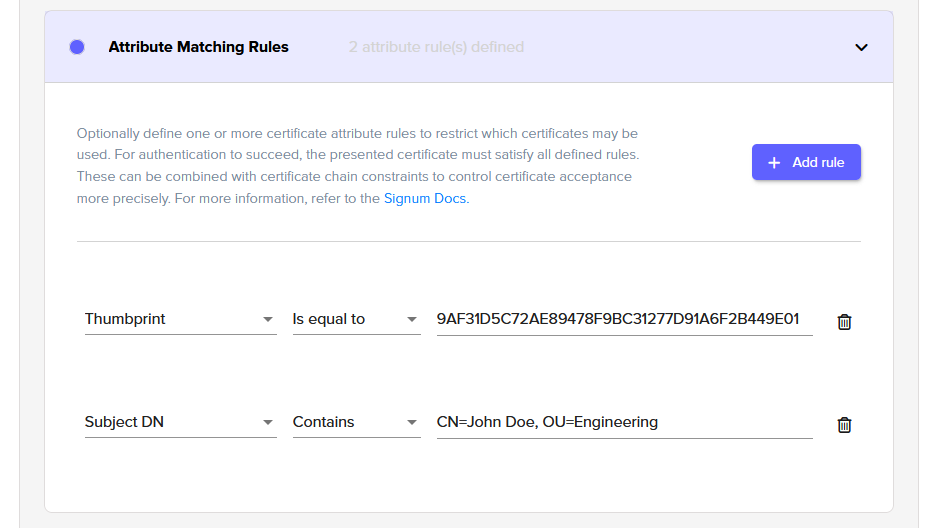
Optionally, define Attribute Matching Rules to enforce during authentication.
Client Certificate Chains
In the Client Certificate Chains setting, define a certificate user by either adding a specific client certificate or adding any client certificate issued by that CA.
Because these entries reference specific certificates, an expired certificate prevents the user from authenticating.
Attribute Matching Rules
In addition to Client Certificate Chains, you can create rules for the user certificate. For example:
Thumbprint is equal to
9AF31D5C72AE89478F9BC31277D91A6F2B449E01Subject DN contains
CN=John Doe, OU=Engineering
To restrict a client certificate to a particular CA, you could add:
Issuer DN is equal to
CN=Example CA, O=Example Corp, C=US
A user is authenticated only if the presented certificate meets all defined Attribute Matching Rules.
The available attributes are:
Serial number
Subject DN
Thumbprint
SANs
Issuer DN
Usage Notes
Any certificate configuration, either Specific Client Certificate or CA Chain, may be only be assigned to one user. Assigning the same configuration to more than one user results in a login error message: “The certificate matches more than one user profile. We’re unable to determine which account to use. Please reach out to your administrator.”
Both the CA certificate chain and the client authentication certificate can be used in combination with attribute matching rules.
Regardless of the situation, expired certificates do not work.
Some example configurations and the resulting behavior are:
Client Certificate Chains | Attribute Matching Rule | Behavior |
|---|---|---|
CA chain | none | An agent presenting with any certificate issued by the CA will be accepted. |
CA chain | ✔️ | An agent presenting with any certificate issued by the CA will be accepted AND the selected attributes must match. |
Client auth cert | none | An agent must present with the specific client certificate. |
Client auth cert | ✔️ | An agent must present with the specific client certificate AND the selected attributes must match. |
.png)