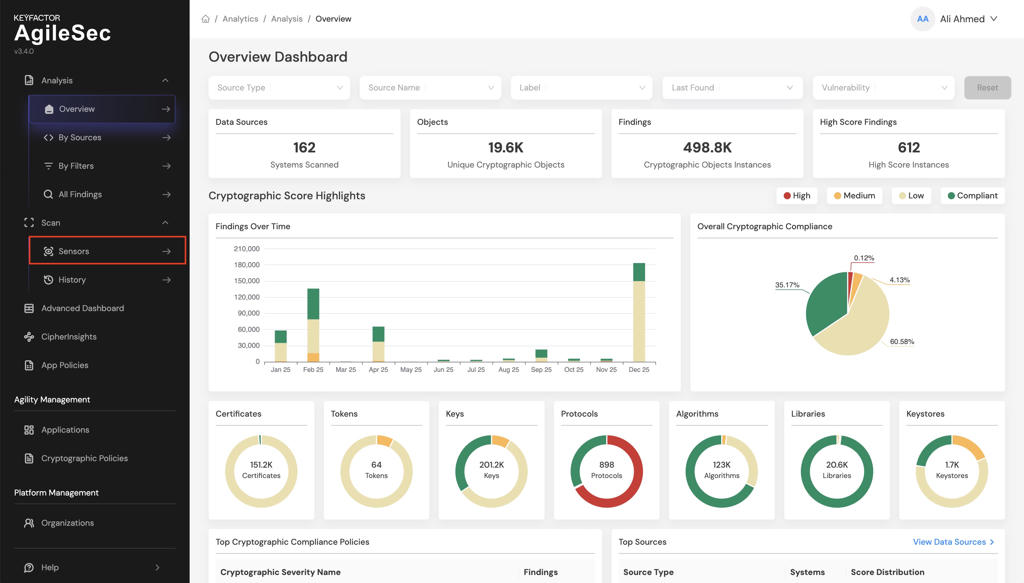
AWSKMS Sensor User Guide
The AWSKMS Sensor User Guide provides instructions for deploying and operating the AWSKMS Sensor within the Keyfactor AgileSec Platform. This guide covers supported authentication methods, execution methods, configuration options, and troubleshooting.
Refer to Sensors Architecture and Overview for additional details on sensor architecture, data flows, incremental scanning, and auto-resolution.
Overview
The AWSKMS Sensor integrates AWS Key Management Service with Keyfactor's AgileSec Platform. This sensor allows you to discover, inventory, and analyze cryptographic keys managed by AWS KMS across your AWS accounts.
Key Features
Key Discovery: Enumerates all KMS keys in a specified AWS region.
Key Metadata Extraction: Retrieves public key information, aliases, and resource tags for each key.
Multi-Key Type Support: Handles symmetric, asymmetric (RSA, ECC), and HMAC key types.
Tag-Based Enrichment: Includes AWS resource tags as metadata on discovered keys.
What Gets Scanned
The sensor queries AWS KMS APIs to discover:
KMS Keys: All customer-managed and AWS-managed keys in the configured region
Public Key Data: RSA and ECC public key material for asymmetric keys
Key Aliases: Human-readable alias names associated with keys
Resource Tags: AWS resource tags applied to KMS keys
Prerequisites
AWSKMS Requirements
Requirement | Details |
|---|---|
Protocol | HTTPS required for AWS API access. |
Access | Network connectivity from the sensor machine to AWS KMS endpoints. |
Credentials | AWS Access Key ID and Secret Access Key with KMS permissions. |
Remote Execution Requirements
If running the unified sensor remotely using CLI:
Component | Requirement |
|---|---|
Operating System |
|
RAM | 3 GB minimum, 4 GB recommended for large repositories |
Disk Space | Minimum 2x Size of your repository. |
Permissions | Read/Write access to working directory |
Supported Authentication Methods
The AWSKMS sensor uses AWS Access Key authentication:
Access Key ID + Secret Access Key: Standard IAM user credentials scoped to the target AWS account and region.
Required Access Rights
The IAM user or role must have the following KMS permissions:
Permission | Purpose | Required |
|---|---|---|
| Enumerate all KMS keys | ✅ Yes |
| Retrieve public key material | ✅ Yes |
| List key aliases | ✅ Yes |
| List resource tags on keys | ✅ Yes |
Running the Sensor
The AWSKMS Sensor can be executed using the following methods:
Platform Scan Execution: Configure and execute scans directly though the Keyfactor AgileSec web UI with on-demand or scheduled execution options.
Using API: Programmatically trigger scans through REST API calls, enabling integration with CI/CD pipelines and automation workflows.
Remote Scan Execution: Deploy and run the sensor via CLI on customer-managed infrastructure for scenarios such as:
Scanning air-gapped or internal instances the platform cannot directly reach
Customers wanting to manage their own scheduling and execution environment.
Refer to Sensors Architecture and Overview: Running the Sensor for additional execution and flow details.
Platform Scan Execution
Running the sensor through the user interface is the simplest and fastest way to get started. The platform enables running on-demand or scheduled scans in a dedicated environment.
Platform Scan Configuration
Step 1: Navigate to Sensors Setup Page
1.1 Open your browser and navigate to the Keyfactor AgileSec Platform Web URL
1.2 Log in with your credentials
1.3 Click on "Sensors" in the navigation bar.
Step 2: Select AWSKMS Sensor
2.1 Click the "Choose a Sensor" button.
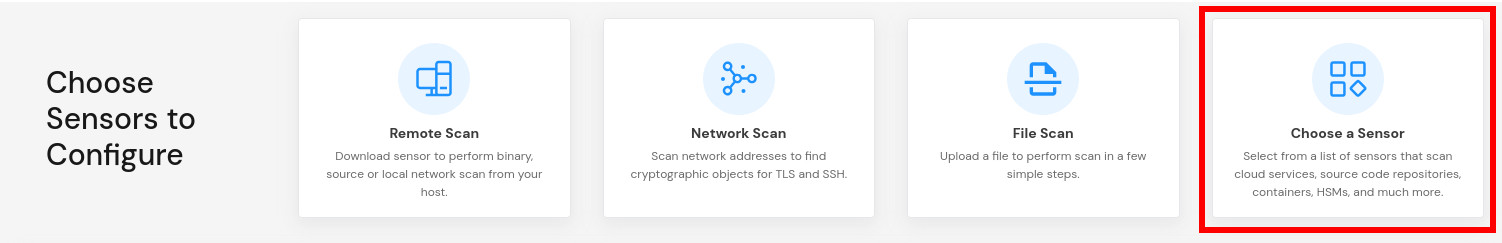
2.2 Browse or search for "AWSKMS"
2.3 Click on the AWSKMS sensor card
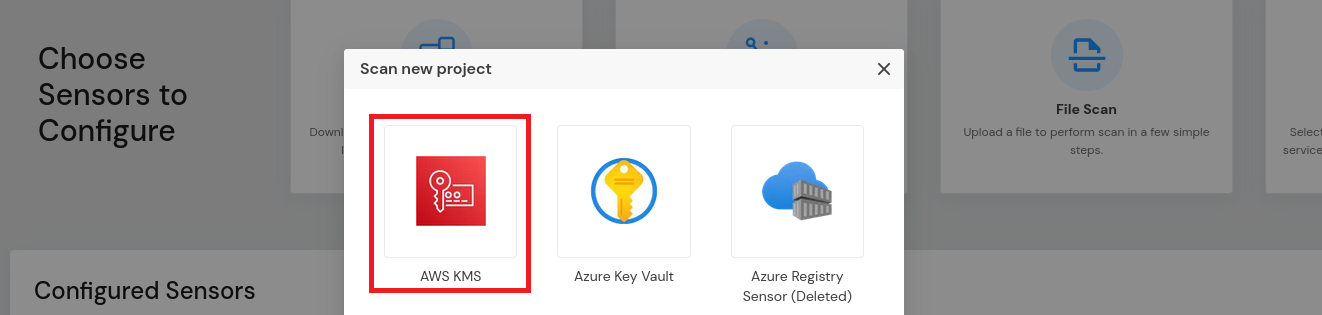
This will open the sensor configuration interface.
Step 3: Configure Sensor Parameters
3.1 Fill in the required configuration parameters:
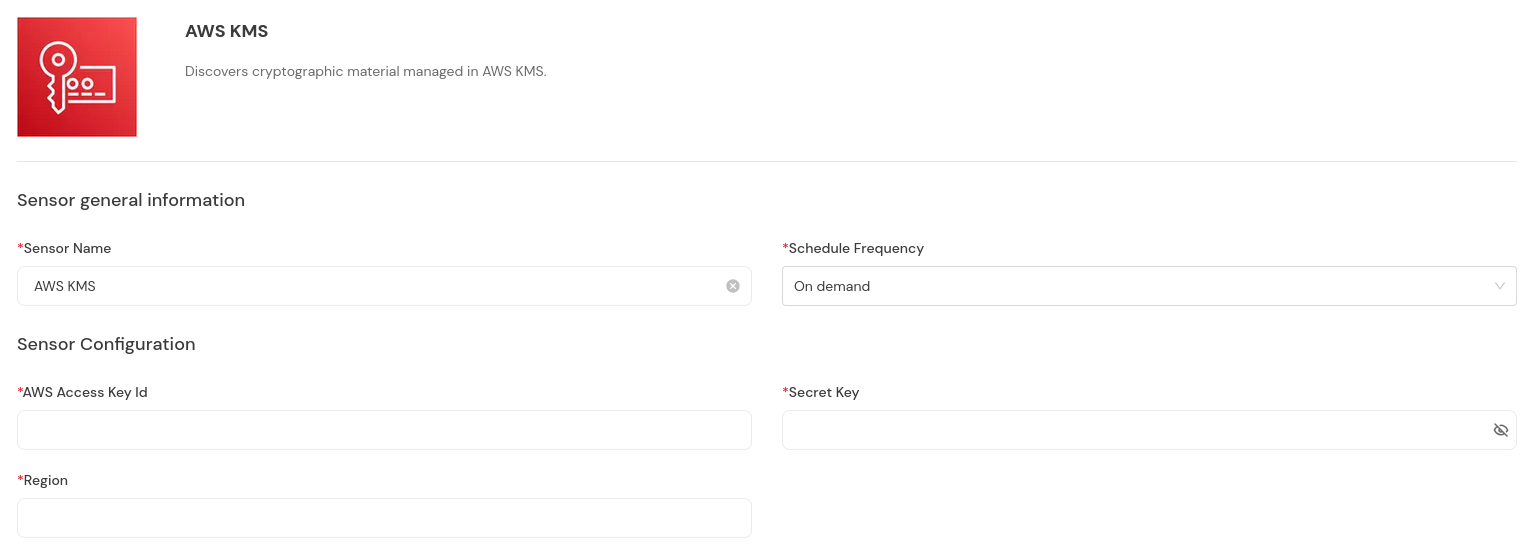
Platform Scan Configuration Fields
Field Name | Display Name | Type | Required | Description |
|---|---|---|---|---|
| Access Key ID | Single-line text | ✅ Yes | AWS Access Key ID for the IAM user |
| Secret Access Key | Password field | ✅ Yes | AWS Secret Access Key for the IAM user |
| AWS Region | Single-line text | ✅ Yes | AWS region to scan (e.g., |
Scan Execution Using API
Scans may be programmatically triggered through REST API calls, enabling seamless integration with CI/CD pipelines, automation workflows, and custom applications. API execution provides flexibility for developers to incorporate cryptographic scanning into their existing development and deployment processes.
Note: For complete API reference, see the API document.
API Access Token
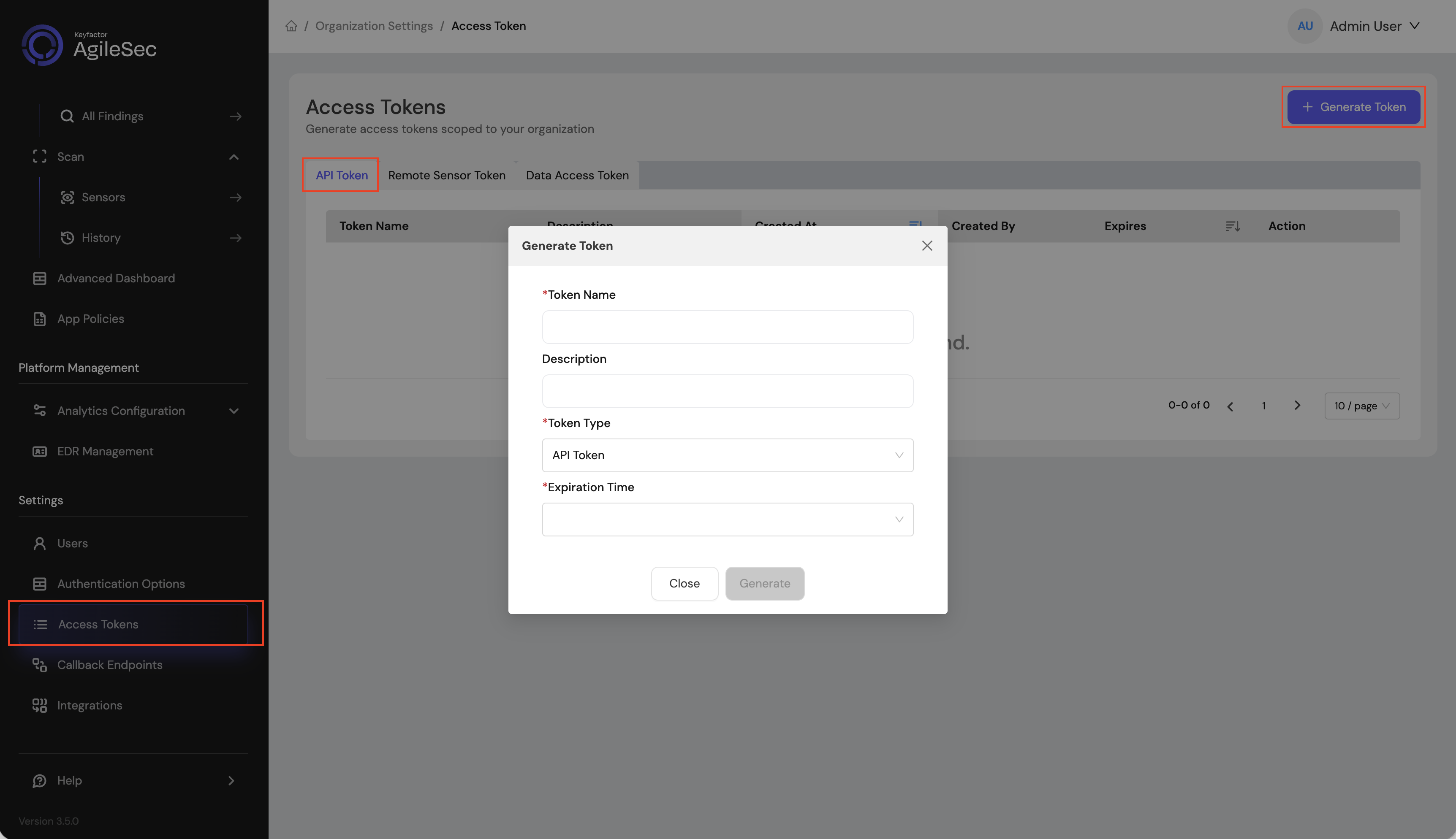
Open your browser and navigate to the AgileSec Platform UI.
Log in with your Keyfactor credentials.
Click "Access Tokens" in the main navigation menu.
Click "Generate Token".
Set Token Type to API Token and provide the required details.
Click "Generate" and copy the generated token.
API Endpoint
POST https://<platform-url>/v3/scan/createRequest Format
Headers
Content-Type: application/json
isg-api-token: <your-api-token>Request Body
The complete request body contains sensor configuration in the sensorConfig field, i.e:
{
"sensorName": "<sensor name>",
"sensorType": "AWS KMS",
"sensorConfig": {
"akid": "<aws access key id>",
"secret_key": "<aws secret key>",
"region": "<aws region>"
},
"callbackId": "<callback id>",
"labels": [
{
"<label name>": "<label value>"
}
],
"priority": "<priority>"
}API Field Descriptions
See Platform Scan Configuration Fields for details.
Remote Scan Execution
Remote Execution Flow allows you to run the sensor on a host using the Unified Sensor binary.
Remote Scan Execution Configuration
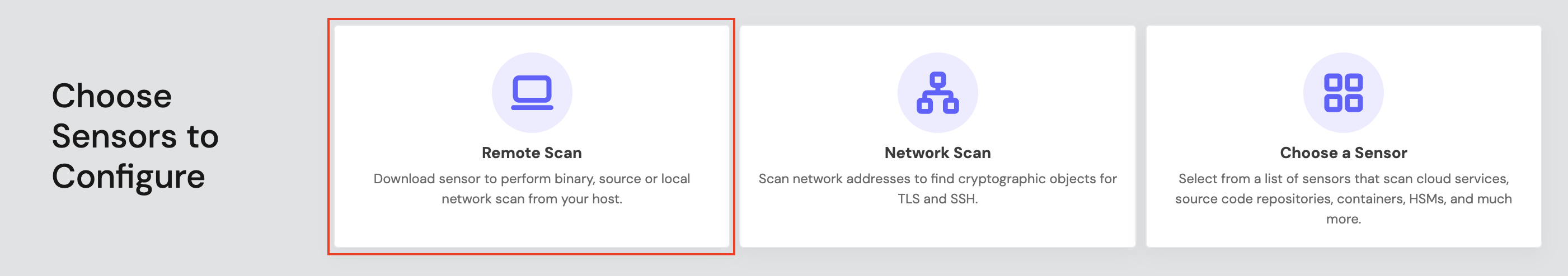
Step 1: Download Unified Sensor
1.1 Navigate to AgileSec Platform UI → Sensors → Remote Scan.
1.2 Download the sensor binary for your operating system.
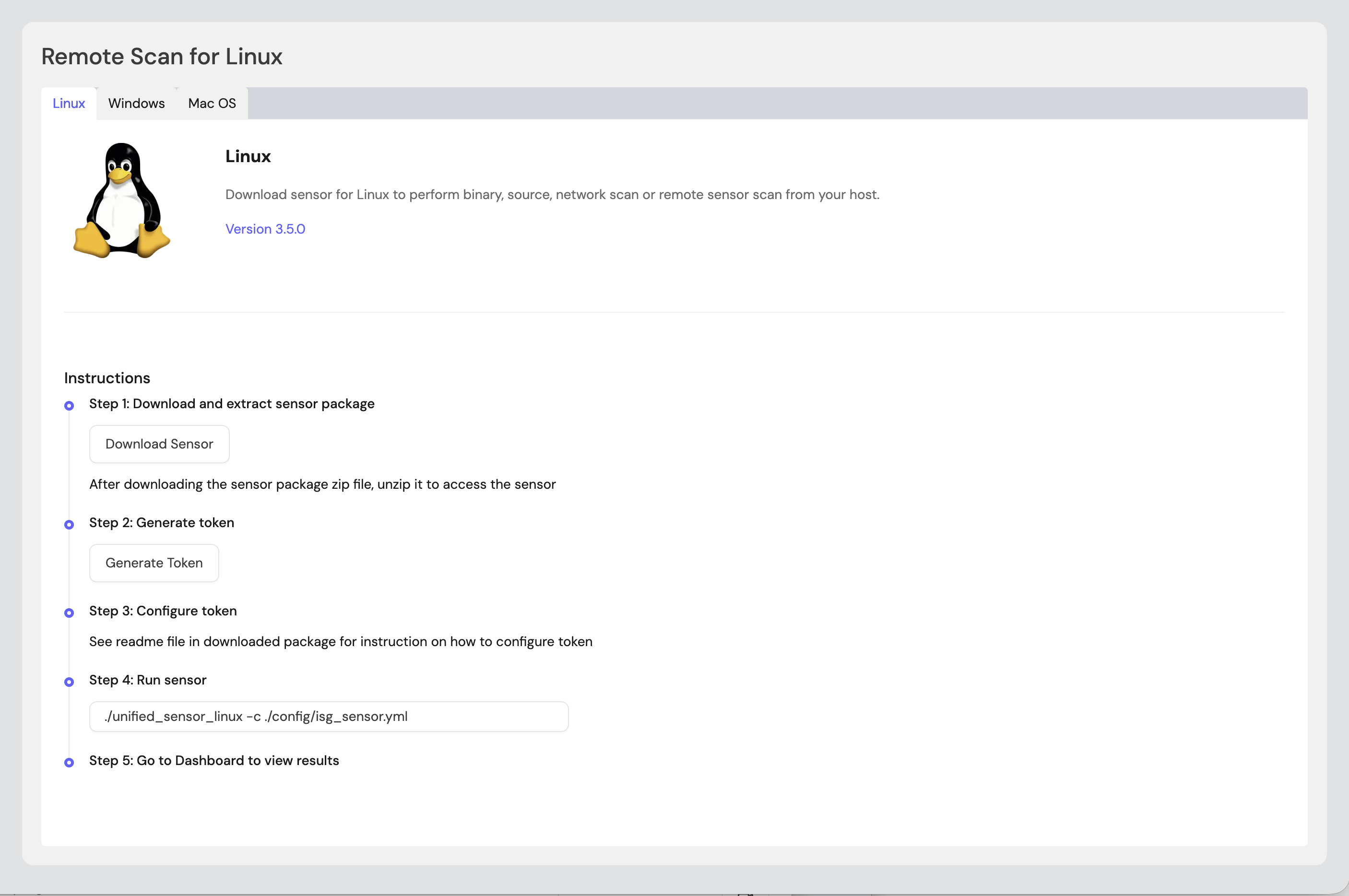
Step 2: Generate Remote Sensor Token
2.1 In the Remote Scan UI, click "Generate Token".
2.2 Copy the generated token.
2.3 Store the token securely in an environment variable or set it in the sensor config:
export SENSOR_TOKEN="your-generated-token"Step 3: Create Configuration File
Create a YAML configuration file (e.g., awskms-config.yml) with your scan settings. An example configuration can be found in config/sample-configs/awskms.yml.
Step 4: Run the Sensor
Execute the sensor with your configuration file:
Linux/macOS
BASH# Set environment variables export SENSOR_TOKEN="your-sensor-token" # Run sensor ./unified_sensor_linux -c awskms-config.ymlWindows (PowerShell)
POWERSHELL# Set environment variables $env:SENSOR_TOKEN = "your-sensor-token" # Run sensor .\\unified_sensor_windows.exe -c .\\awskms-config.yml
Remote Scan Execution Configuration Examples
Basic Configuration
YAMLscan_config: plugins: - awskms - export config: awskms: name: awskms plugin_config: akid: "${env:AWS_ACCESS_KEY_ID}" secret_key: "${env:AWS_SECRET_ACCESS_KEY}" region: "us-east-1"
Known Limitations
Asymmetric Keys Only
Description: Public key material can only be retrieved for asymmetric KMS keys. Symmetric keys are inventoried but their key material is not extractable by design.
Single Region
Description: Each scan covers a single AWS region. To scan multiple regions, configure multiple sensor instances.
Troubleshooting
Common Errors
CONFIG-404— Unable to read/parse configuration fileCause: The configuration file path is incorrect or the file is malformed.
Fix: Verify the config file path and validate JSON syntax.
CONFIG-422— Required attribute not foundCause: A required configuration field (e.g.,
akid,secret_key,region) is missing.Fix: Ensure all required fields are present in the configuration.
AWSKMS-201— FailedListKeysCause: Insufficient IAM permissions or invalid credentials.
Fix: Verify IAM permissions include
kms:ListKeysand credentials are correct.
AWSKMS-202— FailedGetPublicKeyCause: The key may be a symmetric key (no public key) or IAM permissions are insufficient.
Fix: This is expected for symmetric keys. For asymmetric keys, ensure
kms:GetPublicKeypermission.
AWSKMS-203— FailedListAliasesCause: Insufficient IAM permissions.
Fix: Ensure
kms:ListAliasespermission is granted.
AWSKMS-204— FailedListResourceTagsCause: Insufficient IAM permissions.
Fix: Ensure
kms:ListResourceTagspermission is granted.
Getting Support
Collect diagnostic information:
Sensor version
Configuration file (redact credentials)
Log output
AWS details (region, account ID)
Contact Support:
Portal: https://support.keyfactor.com
.png)