The CipherInsights Sensor User Guide provides instructions for deploying and operating the CipherInsights Sensor within the Keyfactor AgileSec Platform. This guide covers supported authentication methods, execution methods, configuration options, and troubleshooting.
Refer to Sensors Architecture and Overview for additional details on sensor architecture, data flows, incremental scanning, and auto-resolution.
Overview
The CipherInsights Sensor integrates InfoSec Global’s CipherInsights with Keyfactor's AgileSec Platform. This sensor allows users to import and analyze cryptographic findings from the CipherInsights API, bringing protocol-level and certificate-level visibility into the AgileSec ecosystem.
Key Features
-
Automated Import: Periodically fetches cryptographic findings from the CipherInsights API.
-
Time-Based Filtering: Scans all available data, or restricts imports to a configurable lookback window (in hours).
-
Paginated Retrieval: Handles large result sets with configurable pagination.
-
TLS Flexibility: Supports disabling certificate validation for non-production environments.
What Gets Scanned
The sensor retrieves findings from the CipherInsights API, including:
-
X.509 Certificates: SSL/TLS certificates discovered by CipherInsights network scans
-
Protocol Information: TLS/SSL protocol versions and cipher suites observed on network endpoints
Prerequisites
CipherInsights Requirements
|
Requirement |
Details |
|---|---|
|
Protocol |
HTTPS required for API access. |
|
Access |
Network connectivity from the sensor machine to the CipherInsights API. |
|
API Access |
A valid CipherInsights API token. |
Remote Execution Requirements
If running the unified sensor remotely using CLI:
|
Component |
Requirement |
|---|---|
|
Operating System |
|
|
RAM |
3 GB minimum, 4 GB recommended for large repositories |
|
Disk Space |
Minimum 2x Size of your repository. |
|
Permissions |
Read/Write access to working directory |
Supported Authentication Methods
The CipherInsights Sensor supports token-based authentication:
-
Obtain an API token from your CipherInsights deployment
-
Provide the token in the sensor configuration via the
tokenfield
Running the Sensor
The CipherInsights Sensor can be executed using the following methods:
-
Platform Scan Execution: Configure and execute scans directly though the Keyfactor AgileSec web UI with on-demand or scheduled execution options.
-
Using API: Programmatically trigger scans through REST API calls, enabling integration with CI/CD pipelines and automation workflows.
-
Remote Scan Execution: Deploy and run the sensor via CLI on customer-managed infrastructure for scenarios such as:
-
Scanning air-gapped or internal instances the platform cannot directly reach
-
Customers wanting to manage their own scheduling and execution environment.
-
Refer to Sensors Architecture and Overview: Running the Sensor for additional execution and flow details.
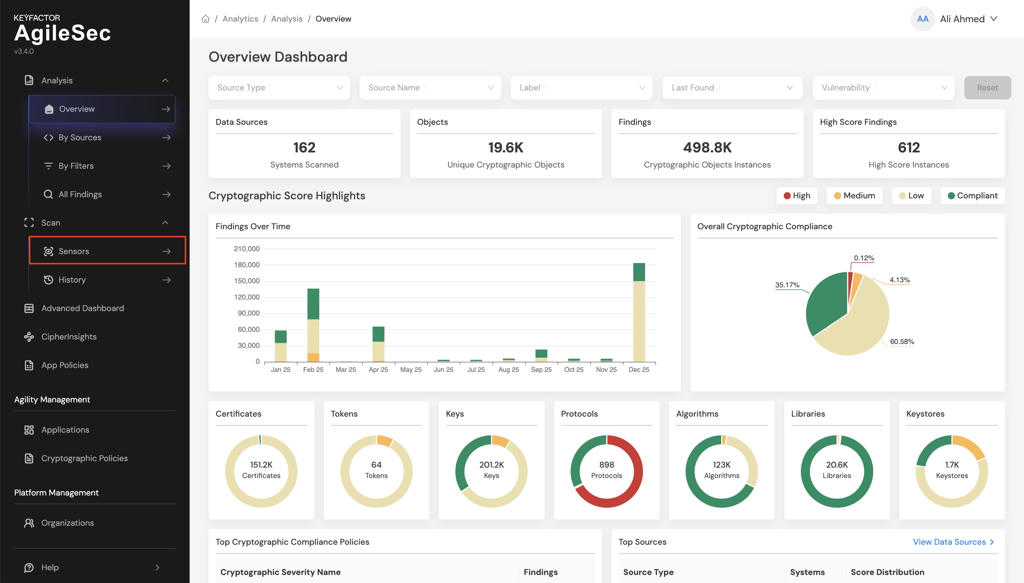
Platform Scan Execution
Running the sensor through the user interface is the simplest and fastest way to get started. The platform enables running on-demand or scheduled scans in a dedicated environment.
Platform Scan Configuration
Step 1: Navigate to Sensors Setup Page
1.1 Open your browser and navigate to the Keyfactor AgileSec Platform Web URL
1.2 Log in with your credentials
1.3 Click on "Sensors" in the navigation bar.
Step 2: Select CipherInsights Sensor
2.1 Click the "Choose a Sensor" button.
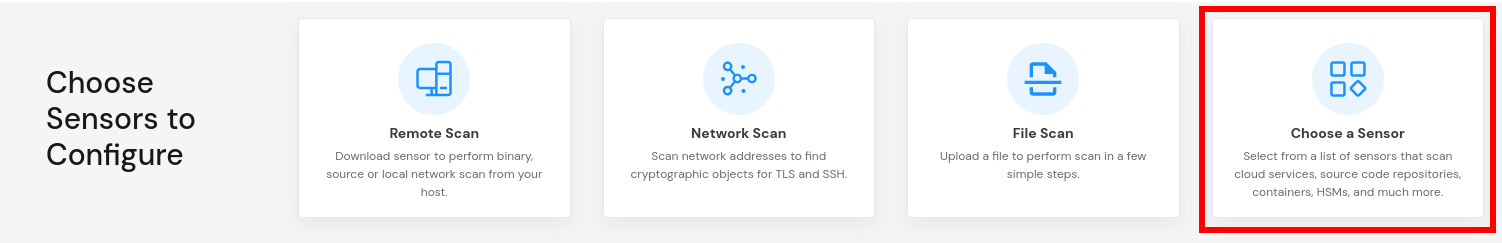
2.2 Browse or search for "CipherInsights".
2.3 Click on the CipherInsights sensor card.
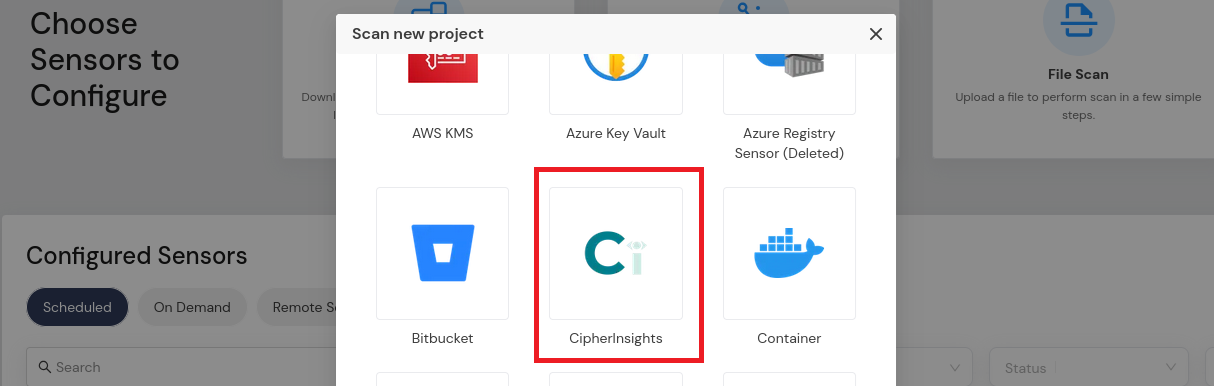
This will open the sensor configuration interface.
Step 3: Configure Sensor Parameters
3.1 Fill in the required configuration parameters:
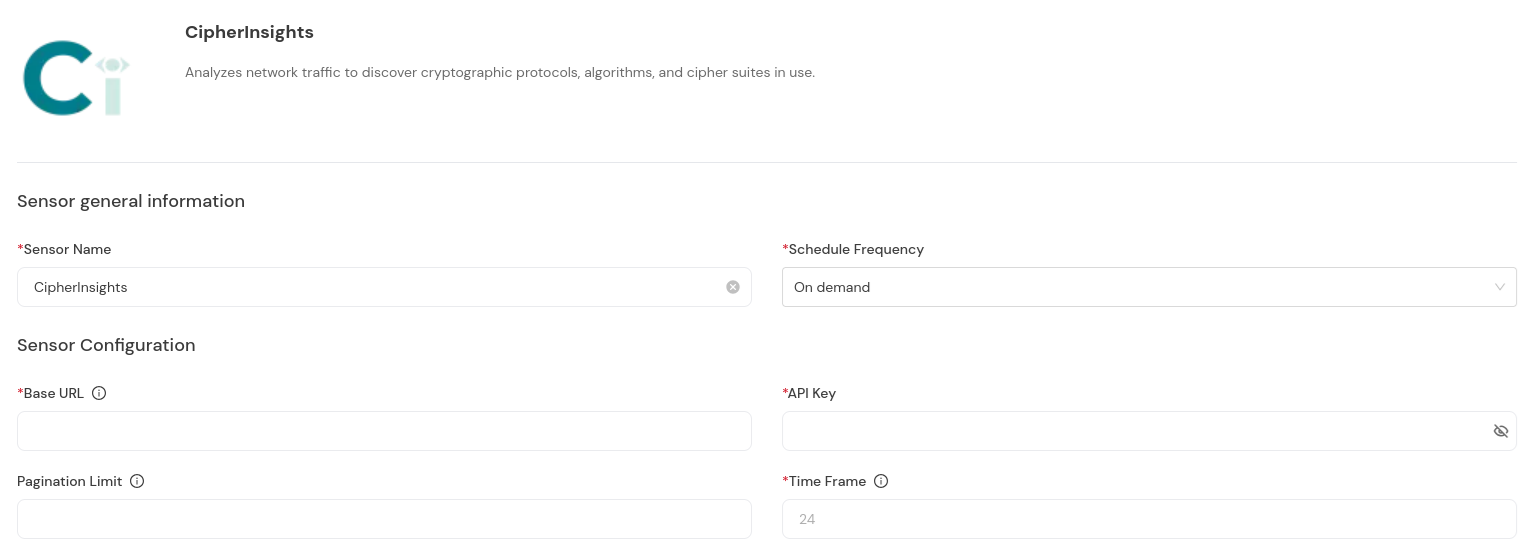
Platform Scan Configuration Fields
|
Field Name |
Display Name |
Type |
Required |
Description |
|---|---|---|---|---|
|
|
API URL |
Single-line text |
✅ Yes |
The base URL of the CipherInsights API |
|
|
API Token |
Password field |
✅ Yes |
Authentication token for the CipherInsights API |
|
|
Time Frame (hours) |
Number |
❌ No |
Scan data from this many hours ago until now. Set to |
|
|
Pagination Limit |
Number |
❌ No |
Number of results per API page |
Scan Execution Using API
Scans may be programmatically triggered through REST API calls, enabling seamless integration with CI/CD pipelines, automation workflows, and custom applications. API execution provides flexibility for developers to incorporate cryptographic scanning into their existing development and deployment processes.
Note: For complete API reference, see the API document.
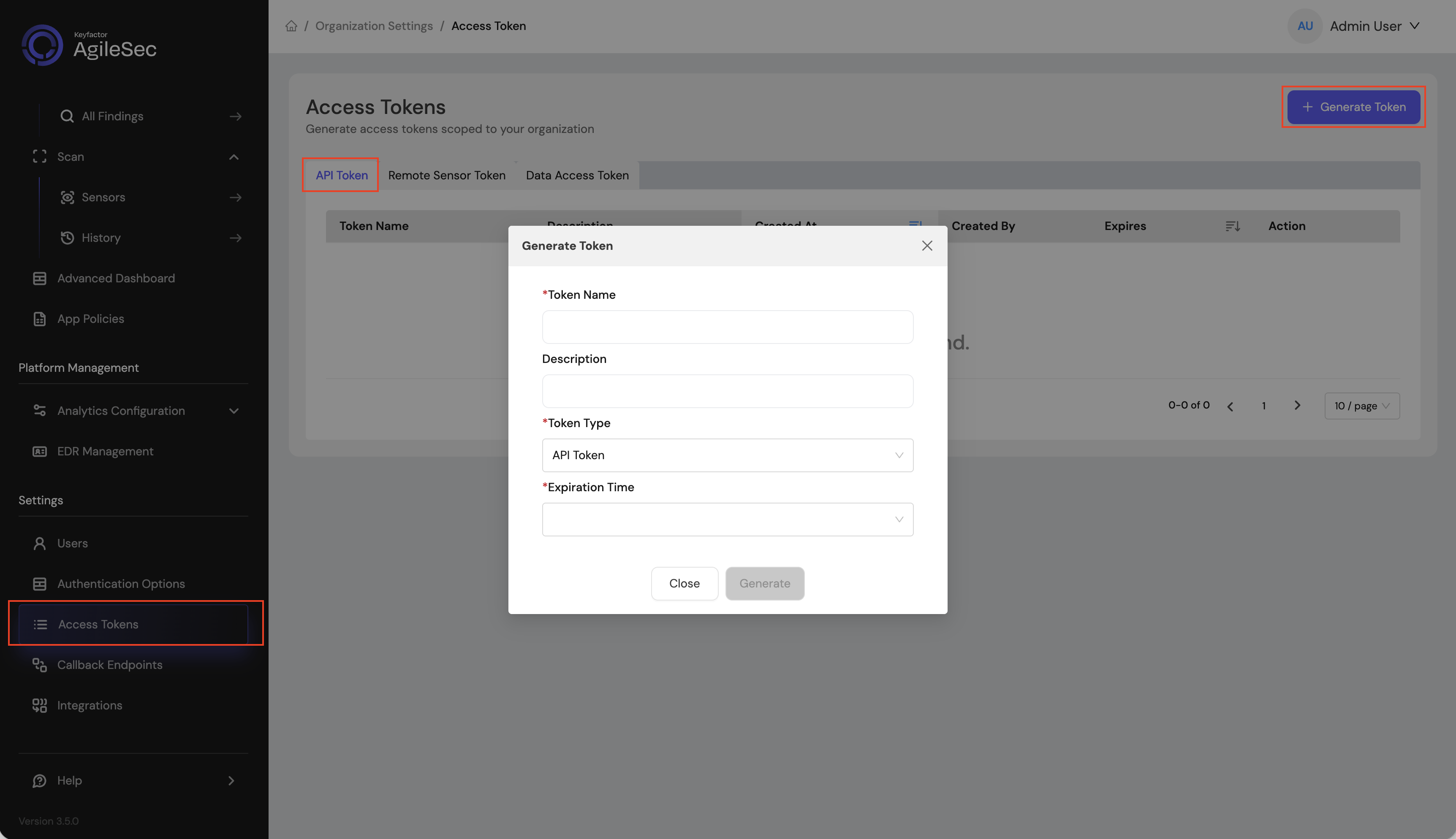
API Access Token
-
Open your browser and navigate to the AgileSec Platform UI.
-
Log in with your Keyfactor credentials.
-
Click "Access Tokens" in the main navigation menu.
-
Click "Generate Token".
-
Set Token Type to API Token and provide the required details.
-
Click "Generate" and copy the generated token.
API Endpoint
POST https://<platform-url>/v3/scan/create
Request Format
Headers
Content-Type: application/json
isg-api-token: <your-api-token>
Request Body
The complete request body contains sensor configuration in the sensorConfig field, i.e:
{
"sensorName": "<sensor name>",
"sensorType": "CipherInsights",
"sensorConfig": {
"url": "<cipher insights api url>",
"token": "<api token>",
"time_frame": 24,
"pagination_limit": 100
},
"callbackId": "<callback id>",
"labels": [
{
"<label name>": "<label value>"
}
],
"priority": "<priority>"
}
API Field Descriptions
See Platform Scan Configuration Fields for details.
Remote Scan Execution
Remote Execution Flow allows you to run the sensor on a host using the Unified Sensor binary.
Remote Scan Execution Configuration
Step 1: Download Unified Sensor
1.1 Navigate to AgileSec Platform UI → Sensors → Remote Scan.
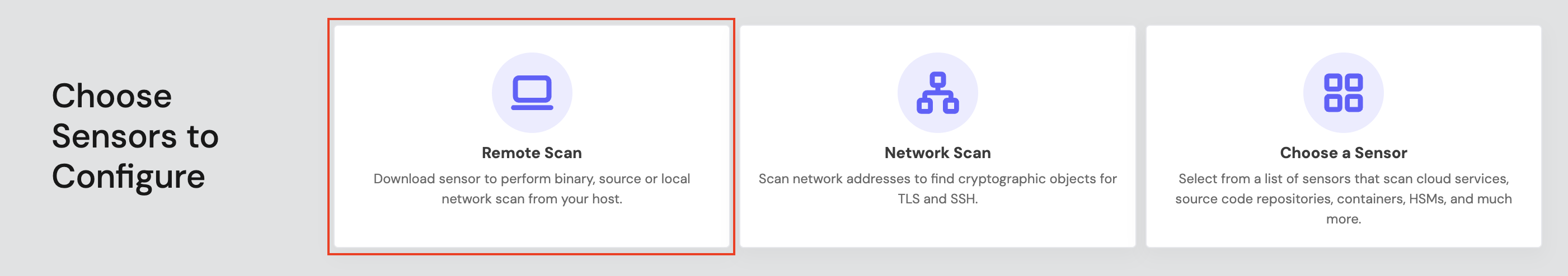
1.2 Download the sensor binary for your operating system.
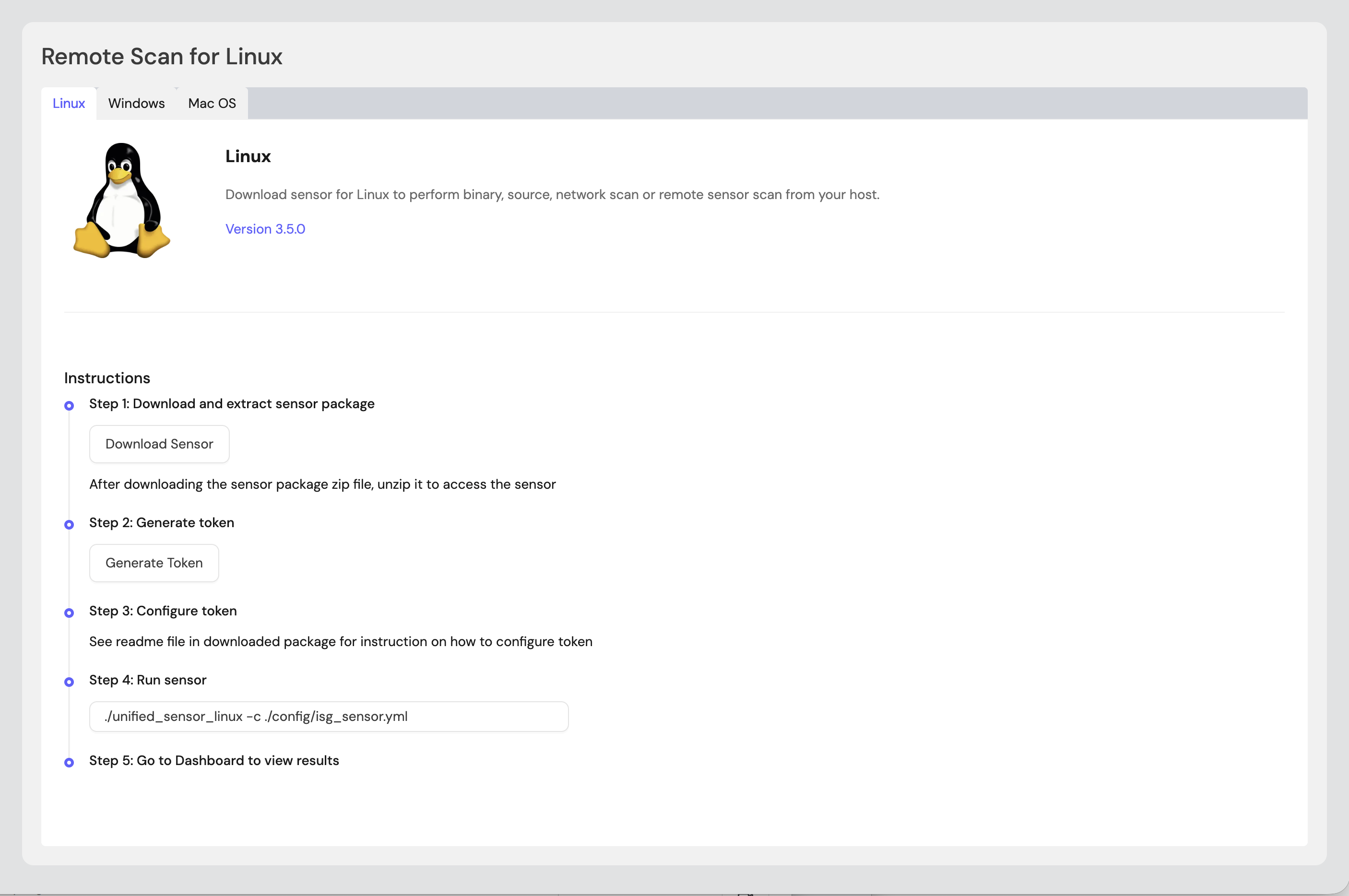
Step 2: Generate Remote Sensor Token
2.1 In the Remote Scan UI, click "Generate Token".
2.2 Copy the generated token.
2.3 Store the token securely in an environment variable or set it in the sensor config:
export SENSOR_TOKEN="your-generated-token"
Step 3: Create Configuration File
Create a YAML configuration file (e.g., cipher_insights-config.yml) with your scan settings. An example configuration can be found at config/sample-configs/cipher_insights.yml.
Step 4: Run the Sensor
Execute the sensor with your configuration file:
-
Linux/macOS
Bash# Set environment variables export SENSOR_TOKEN="your-sensor-token" # Run sensor ./unified_sensor_linux -c cipher_insights-config.yml -
Windows (PowerShell)
PowerShell# Set environment variables $env:SENSOR_TOKEN = "your-sensor-token" # Run sensor .\\unified_sensor_windows.exe -c .\\cipher_insights-config.yml
Remote Scan Execution Configuration Examples
-
Basic Configuration
YAMLscan_config: plugins: - cipher_insights - export config: cipher_insights: name: cipher_insights plugin_config: url: "<https://cipherinsights.example.com/api/v1/>" token: "${env:CI_TOKEN}" insecure: false -
With Time Frame and Pagination
YAMLscan_config: plugins: - cipher_insights - export config: cipher_insights: name: cipher_insights plugin_config: url: "<https://cipherinsights.example.com/api/v1/>" token: "${env:CI_TOKEN}" insecure: false time_frame: 24 pagination_limit: 200
The insecure field skips TLS verification. Set to true to skip certificate validation when connecting to the CipherInsights API.
Known Limitations
API Rate Limiting
-
Description: The CipherInsights API may enforce rate limits depending on deployment configuration.
-
Impact: Large datasets may require pagination tuning.
-
Workaround: Adjust
pagination_limitandtime_frameto manage request volume.
Troubleshooting
Common Errors
-
CONFIG-404— Unable to read/parse configuration file-
Cause: The configuration file path is incorrect or the file is malformed.
-
Fix: Verify the config file path and validate JSON syntax.
-
-
CONFIG-422— Required attribute not found-
Cause: A required configuration field (e.g.,
urlortoken) is missing. -
Fix: Ensure all required fields are present in the configuration.
-
-
401 Unauthorized-
Cause: Invalid or expired API token.
-
Fix: Verify the token is correct and has not expired.
-
-
Connection refusedor TLS errors-
Cause: Network connectivity issue or certificate validation failure.
-
Fix: Ensure the sensor can reach the CipherInsights API. When using remote scan, set
insecure: truefor self-signed certificates.
-
Getting Support
Collect diagnostic information:
-
Sensor version
-
Configuration file (redact tokens)
-
Log output
-
CipherInsights deployment details (URL, version)
Contact Support:
-
Portal: https://support.keyfactor.com
.png)