Creating a Chimera CA
The following outlines how to create a Chimera X509 Root CA.
A Chimera Certificate Authority (CA) is an X509 CA with two key pairs and two signing algorithms, where a combination of classic algorithms and quantum-safe algorithms are used.
For more general information on Chimera CAs, see Chimera CA.
To create a Chimera X509 Root CA in EJBCA, do the following:
Create Crypto Token and keys
To create a Chimera Root CA crypto token and keys, follow these steps:
In the EJBCA menu, under CA Functions, click Crypto Tokens to open the Manage Crypto Tokens page.
Click Create new and specify the following on the New Crypto Token page:
Name: Specify a name for the Chimera CA crypto token.
Type: Select Soft to create a soft crypto token.
Authentication Code: Enter a password to be used to activate the crypto token. Remember this password.
Click Save to create the Root CA crypto token.
Next, generate three CA keys:
Generate a classic algorithm signKey, for example using RSA 2048, by specifying a name, algorithm, key specification, and then click Generate new keypair.
Generate a quantum-safe algorithm signKeyAlternative, for example using DILITHIUM2, by specifying a name, algorithm, key specification, and then click Generate new keypair.
Generate a classic algorithm testKey, for example using RSA 2048, by specifying a name, algorithm, key specification, and then click Generate new keypair.
Generate a defaultKey, using RSA 2048, by specifying a name name, algorithm, key specification, and then click Generate new keypair.
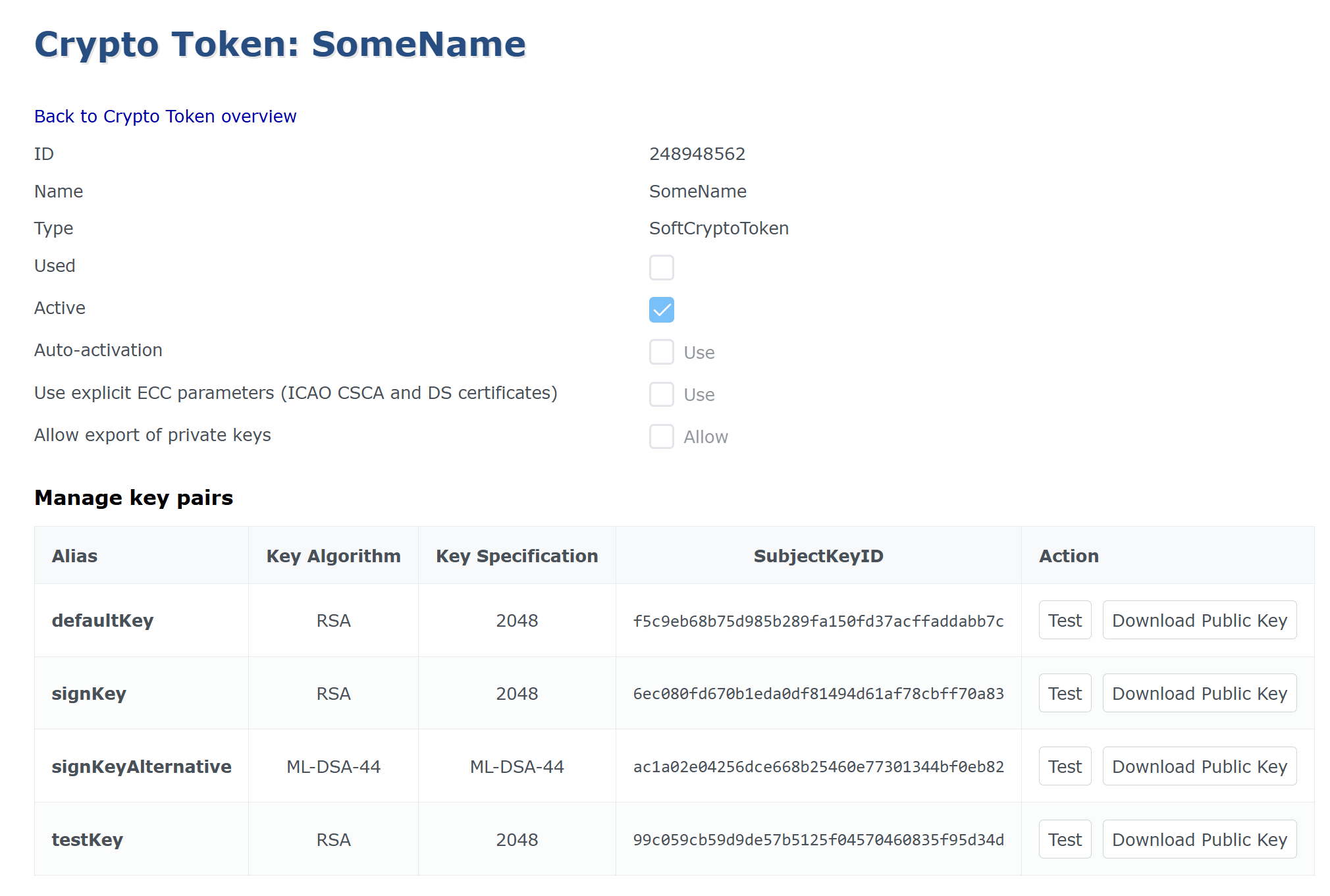
You have now created the Root CA crypto token and keys.
Create Chimera Root CA
To create the Chimera Root CA, follow these steps:
In the EJBCA menu, under CA Functions, click Certification Authorities to open the Manage Certificate Authorities page.
In the Add CA field, specify a name for the CA and click Create.
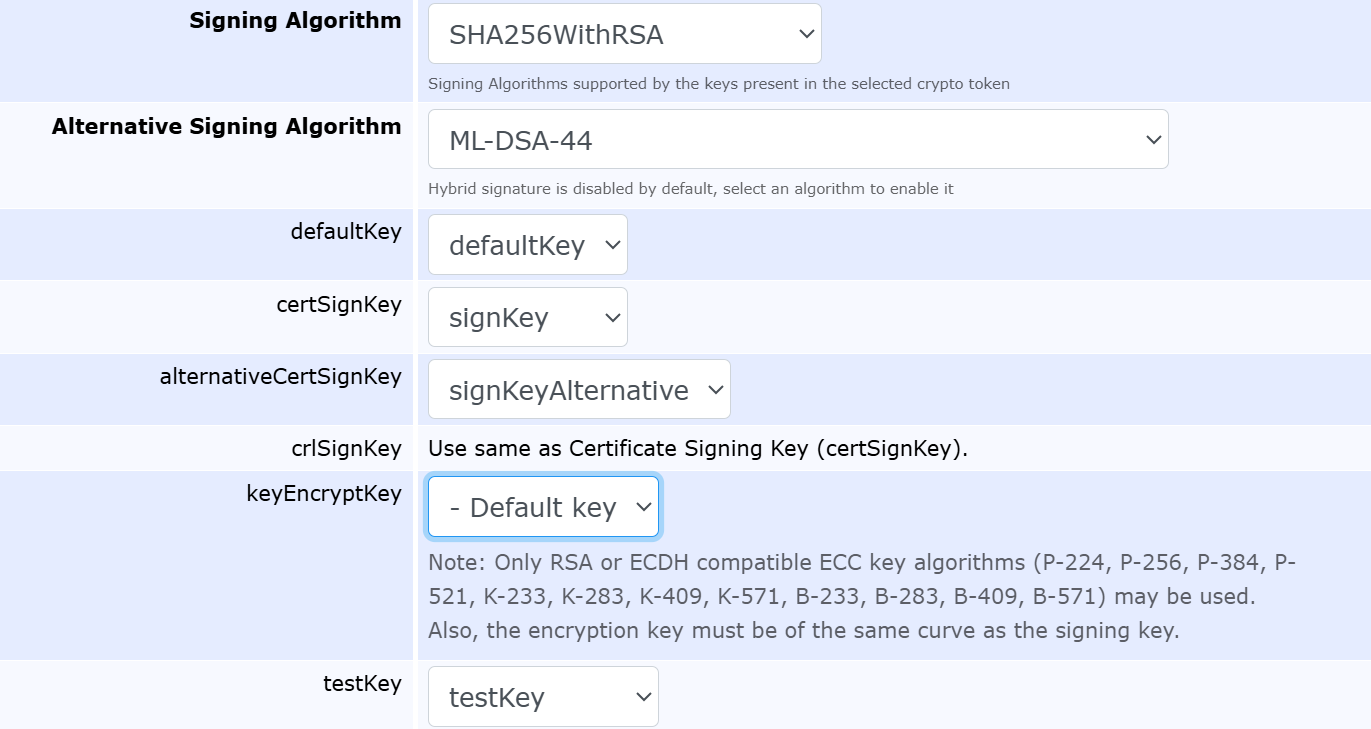
On the Create CA page, update the following:
In the Crypto Token list, select the hybrid CA crypto token you created earlier.
For Alternative Signing Algorithm, select a quantum-safe Alternative Signing Algorithm, for example DILITHIUM2, and verify that the certSignKey, alternativeCertSignKey, defaultKey and testKey are set correctly.
Under CA Certificate Data, specify the following:
Subject DN: Specify the subject DN for the CA.
Signed by: Verify that Self Signed is selected since this is the Root CA. Self Signed means that this CA has signed itself, thus making it a Root CA.
Certificate Profile: Select a certificate profile. The certificate profile can either be the ROOTCA template, or a derivative of it.
Validity: Specify the Validity of the CAs certificate. In this example, 10 y.
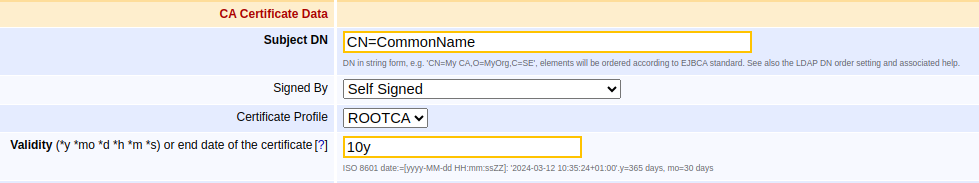
Click Create to create the hybrid Root CA.
Your hybrid Root CA is now online and listed on the Manage Certificate Authorities page.
.png)